Discover essential security-first architecture strategies to help developers build resilient, impact-driven web solutions.

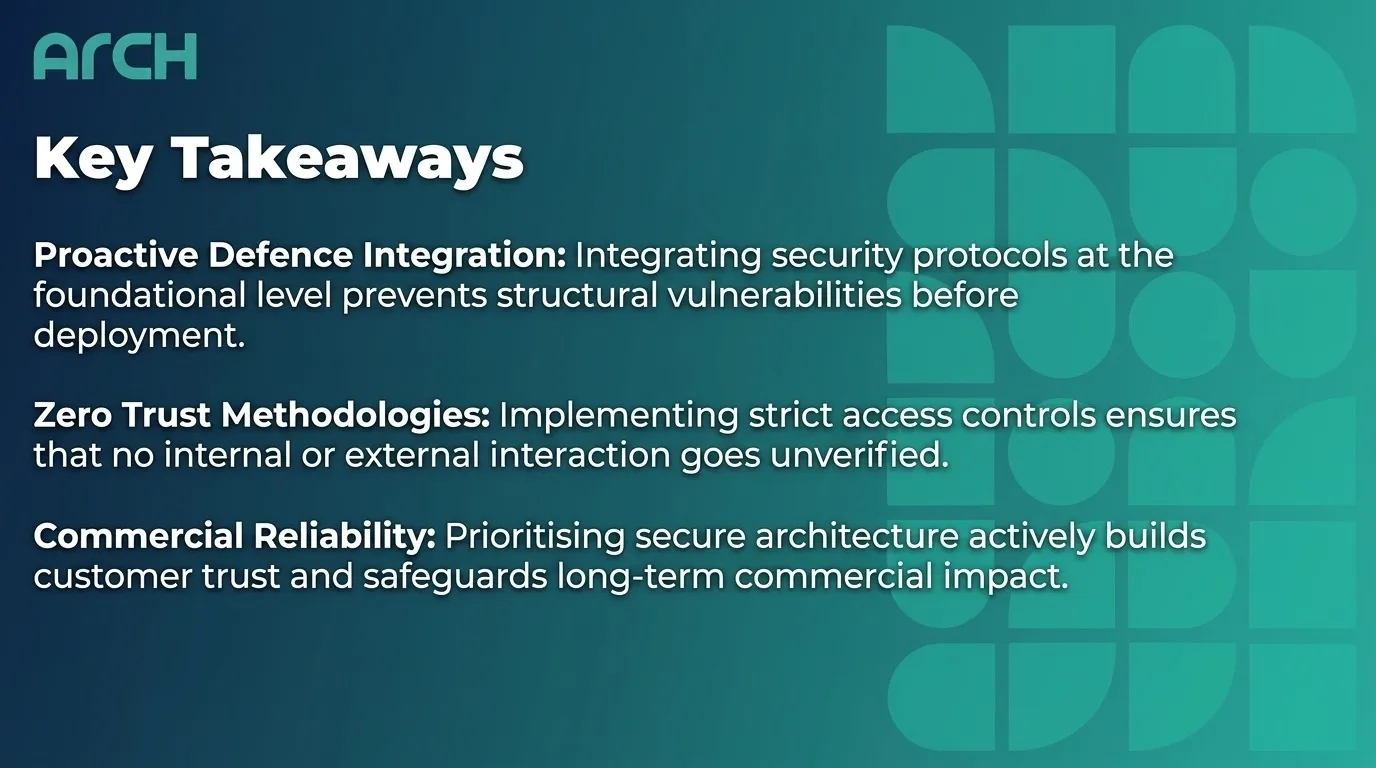
Key Takeaways
-
Proactive Defence Integration: Integrating security protocols at the foundational level prevents structural vulnerabilities before deployment.
-
Zero Trust Methodologies: Implementing strict access controls ensures that no internal or external interaction goes unverified.
-
Commercial Reliability: Prioritising secure architecture actively builds customer trust and safeguards long-term commercial impact.
Establishing a Security-Centric Foundation
In today’s hyper-connected environment, building robust web applications requires more than just clean code and appealing user interfaces. Security can no longer be treated as a final-stage add-on; it must be fundamentally woven into the fabric of the software architecture. This proactive paradigm is rapidly becoming the industry standard for impact-driven development.
As businesses look to expand their online footprint, they face an increasingly sophisticated array of digital threats. From mobile applications to complex web portals, every touchpoint must be fortified against malicious behaviour. Adopting a structural approach ensures that technology serves as a reliable enabler of growth rather than a potential commercial liability.
To navigate these technical challenges effectively, modern businesses are turning to collaborative experts who prioritise structural integrity. By partnering with a dedicated website app and website developers, organisations can seamlessly integrate secure practices into their core development programme. This human-centred innovation ultimately delivers resilient solutions that foster lasting user trust.
Embedding Defence at the Code Level
The journey toward resilient web architecture begins at the earliest stages of the software development lifecycle. Developers must rigorously evaluate third-party libraries and frameworks to prevent inheriting external vulnerabilities. Implementing automated scanning tools within the continuous integration pipeline allows teams to analyse code continuously without stifling ambitious innovation.
Furthermore, adopting secure coding standards establishes a unified language of defence across the entire engineering team. When developers view security as a shared, collaborative responsibility, the overall structural integrity of the application improves drastically. This purposeful alignment reduces technical debt and minimises the likelihood of severe post-launch disruptions.
It is also crucial to establish robust error handling and logging protocols from the outset of the build. By ensuring systems fail securely, developers prevent sensitive diagnostic data from leaking to unauthorised users. Ultimately, these technical measures lay the groundwork for a platform that confidently withstands rigorous real-world usage.
Embracing Zero Trust Principles
The traditional perimeter-based security model is no longer sufficient for modern, highly distributed web applications. Zero Trust architecture operates on a simple but critical premise: trust nothing, verify everything. By mandating rigorous identity authentication at every single access request, developers severely limit potential attack surfaces.
Applying this model requires implementing strict, least-privilege access controls across both user interfaces and backend APIs. Whether a request originates from an internal server or a remote mobile application, it must be comprehensively validated against real-time behavioural signals. This strategy not only thwarts unauthorised lateral movement but also centralises system-wide access governance.
Ultimately, a Zero Trust approach aligns seamlessly with human-centred design by protecting user data without introducing unnecessary friction. It allows expert partners to deliver ambitious digital solutions that remain intrinsically protected against compromised credentials. Such strategies are fundamental to maintaining operational continuity in a progressively hostile digital landscape.
The Commercial Value of Robust Architecture
While security is fundamentally a technical requirement, its overarching value is deeply commercial and reputation-based. A data breach can inflict irreversible damage on a brand’s public standing, actively unravelling years of hard-won consumer trust. Conversely, digital platforms that demonstrably prioritise user safety naturally command greater market confidence and brand loyalty.
Impact-driven organisations recognise that resilient infrastructure is a powerful competitive differentiator. Consumers are increasingly aware of data privacy issues and actively gravitate toward businesses that visibly champion secure digital environments. Investing in foundational security thereby transforms a defensive necessity into a proactive catalyst for sustainable digital growth.
Regular compliance audits and transparent security practices further solidify this distinct commercial advantage. When companies actively collaborate with expert technologists to optimise their security posture, they signal a profound commitment to long-term quality. This strategic foresight is what separates truly resilient businesses from their highly vulnerable competitors.
Conclusion
Building robust digital solutions requires an unwavering commitment to security at every layer of the architectural stack. By shifting defence strategies to the very beginning of the development lifecycle, teams can effectively neutralise threats before they materialise. This deliberate methodology ensures that the final product remains both secure and exceptionally functional.
In an era defined by rapid technological shifts, foundational security acts as the bedrock for true human-centred innovation. Organisations must view this approach not as a restrictive hurdle, but as an essential enabler of sustainable, ambitious expansion. Embracing a security-first mindset is the definitive strategy for navigating the complexities of the modern web ecosystem.
Frequently Asked Questions
What does a security-first architecture entail? It involves integrating security protocols and vulnerability assessments into the earliest stages of software design. Rather than applying protective measures retrospectively, this approach weaves defence directly into the foundational codebase.
How does Zero Trust improve web application resilience? Zero Trust principles mandate that every single network request must be thoroughly authenticated and authorised, regardless of its origin. This significantly reduces the risk of internal breaches and limits the scope of any potential cyber intrusion.
Why is proactive security considered a commercial advantage? By safeguarding user data and ensuring uninterrupted service, proactive security measures directly foster consumer trust and loyalty. This robust protection protects brand reputation and provides a reliable foundation for long-term operational success.

